HEXA OSINT CTF V2
1. Summary
| Event | HEXA OSINT CTF V2 |
| Organizer | HEXA |
| Dates | From 27/01/2023 to 29/01/2023 |
| Type and Format | Jeopardy, OSINT-only, remote |
| Team Name | Holy fun king bingle :3 |
| Rank | 14/117 |
2. CTF and Organizer
The HEXA OSINT CTF V2 was the second part of a CTF held from January 27 to 29, 2023, organized by the HEXA association, with the particularity of being structured as an investigation with fictional characters. No pwn or reverse engineering challenges here, only OSINT skills required. 🔍
The full case was designed to unfold across three parts. However, we didn’t have time to participate in the final CTF, HEXA OSINT CTF V3, that happened in 2024.

3. Story
The outcome of HEXA OSINT CTF V1 led to the arrest of a group of activists called Manipar, who were stealing data from sensitive sectors like military and banking. Their leader was a woman named Lucilhe Dumarquais. However, she disappeared during a prison transfer. The objective is to track her down.
4. Characters
The challenges were organized around fictional characters.
Lucilhe Dumarquais
- Role: Manipar’s leader and target of the Bruised Rogue mission
- Social medias:
- Viadeo: https[:]//viadeo.journaldunet[.]com/p/lucilhe-dumarquais-7961888
Lian Nussbaumer, the Lawyer
- Role: Mastermind, tax lawyer and legal owner of Nexelat
- Location: Zurich, Suisse
- Interests: Trading
- Email addresses:
mastermind_mastermind@proton.me - Usernames: nelexlian, Mind_master
- Social medias:
- LinkedIn: https[:]//www.linkedin[.]com/in/lian-nussbaumer-92b89b253/
- eToro (trading): https[:]//www.etoro[.]com/people/nelexlian
- OpenSea.io: https[:]//opensea[.]io/Mind_master/
Olga Vokolska, the Developer
- Role: Developed Nexelat’s website
- Age: 19
- Family members: Oleg Vokolski (father)
- Email addresses:
vok_0lski@proton.me - Usernames: OVokolska, littleSparr0w
- Social medias:
- GitHub: https[:]//github[.]com/OVokolska
- Mastodon: https[:]//cyberplace[.]social/@littlesparr0w
Oleg Vokolski, Action Man
- Role: Robber recruited to help Lucilhe Dumarquais escape and bring her to Tsuzune Yokoyama
- Family members: Olga Vokolska (daughter)
Minca H., the Associate
- Height: 1.87m
- Email addresses:
mincah_mm@proton.me - Usernames: mincah_mmt
- Social medias:
- TripAdvisor: https[:]//www.tripadvisor[.]com/Profile/mincah_mm
Tsuzune Yokoyama, the Client
- Role: Nexelat’s client, ordered Lucilhe Dumarquais’ exfiltration
- Email addresses:
tsuyo63@proton.me - Usernames: tsuyo63
5. Challenges
1. The Lawyer
The Law Firm
- On LinkedIn, we can see that a member works at Nexelat in Zurich. Their name is redacted.
- Let’s suppose it is a Swiss company ->
.chTLD ->nexelat.chexists. - Interesting page to keep in mind: http[:]//www.nelexat[.]ch/index.php/author/admin4847/
The Lawyer
- On this page, we learn that Lian Nussbaumer is Nelexat legal owner: http[:]//www.nelexat[.]ch/index.php/terms/
- https[:]//www.linkedin[.]com/in/lian-nussbaumer-92b89b253/ -> He studied at Neuchâtel Law University.
- Interesting pages to keep in mind:
- https[:]//www.linkedin[.]com/posts/lian-nussbaumer-92b89b253_taxlaw-taxlawyer-taxdefense-activity-7023577151375331328-LW1p
- https[:]//www.linkedin[.]com/posts/lian-nussbaumer-92b89b253_tax-taxlaw-activity-7023681375656443904-6fr0
Alias
- On Lian Nussbaumer’s LinkedIn page, we find this post: https[:]//www.linkedin[.]com/posts/lian-nussbaumer-92b89b253_tax-taxlaw-activity-7023681375656443904-6fr0
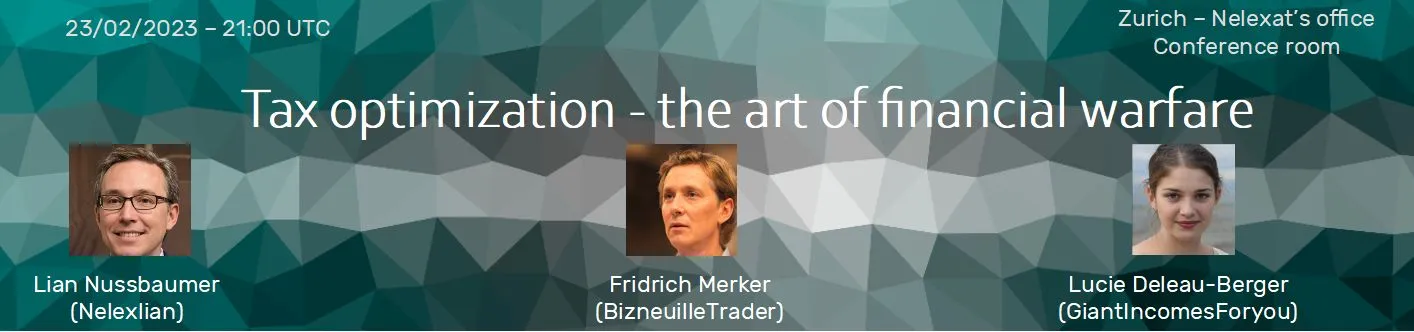
- We supposed Nelexlian is one of his usernames and decided to search on the most famous e-trading platforms. eToro is apparently the most used: https[:]//www.etoro[.]com/people/nelexlian -> Flag in the bio.
Trustworthy
- https[:]//www.nelexat[.]ch/index.php/wp-json/wp/v2/pages
- An email address can be found in the certificate.
Experts
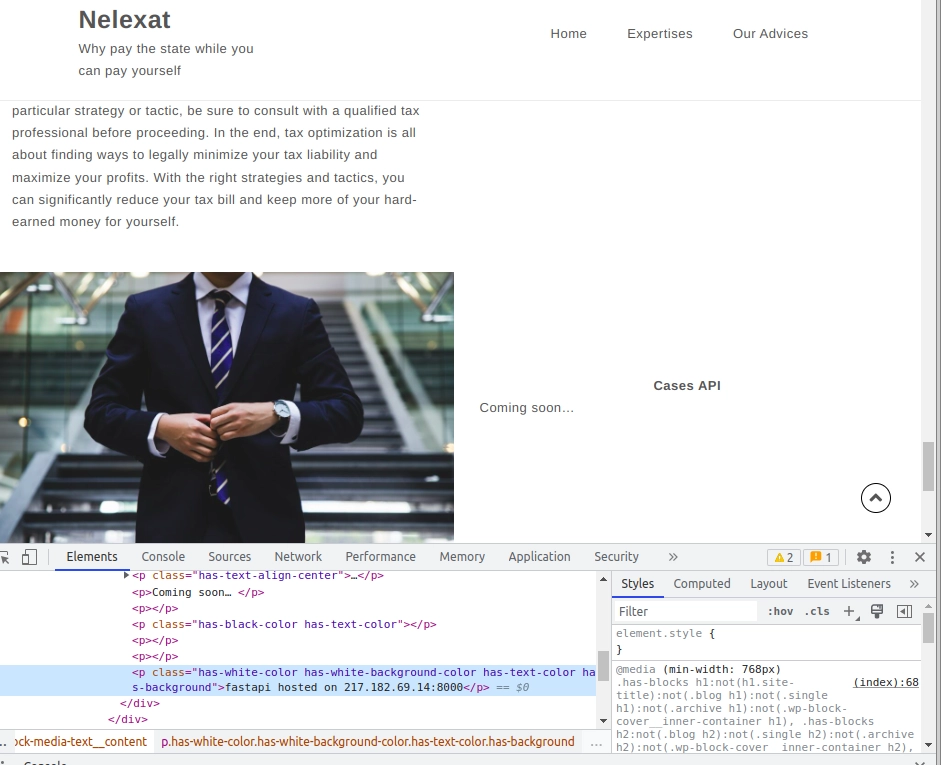
- Nexelat’s website relies on FastAPI which exposes an interactive documentation, by default at
/docs.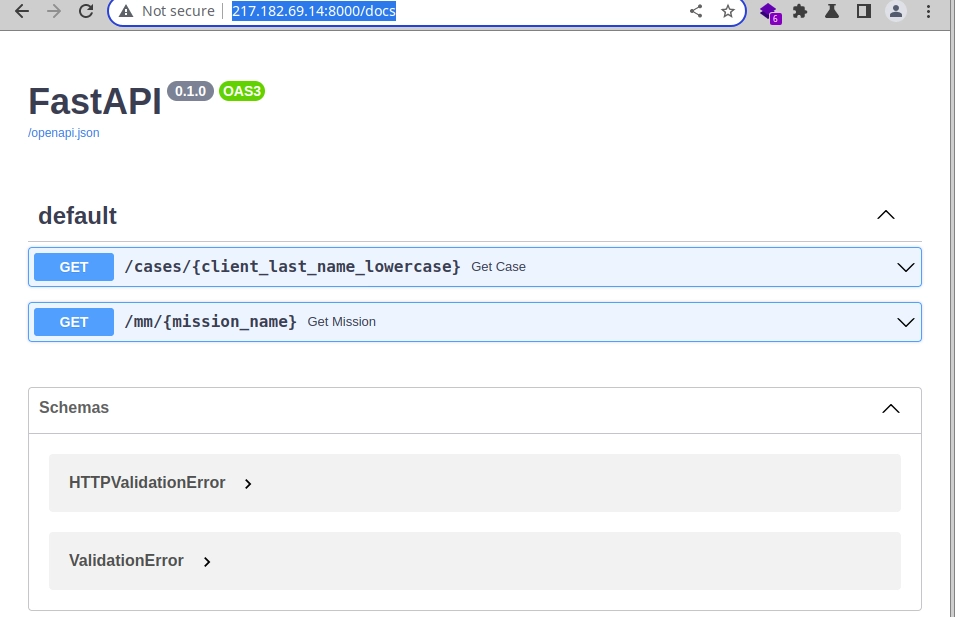
- Searching “dumarquais”:
http://217.182.69.14:8000/cases/%7Bclient_last_name_lowercase%7D?name=dumarquaisgives the following result:{ "name": "dumarquais", "description": "This case is related to Lucilhe Dumarquais, head of Manipar organisation, which was organizing a data trafic. After a bitter battle with the opposing lawyers, I managed to get a lighter sentence in a prison in France, without my client having to give any information about the people she was working with. HEXA{s3cure_y0ur_d4mn_4p1}" }
Herbaceous
- Searching
mastermind_mastermind@proton.mevia Epieos, we get a Google agenda (https[:]//calendar.google[.]com/calendar/u/0/embed?src=mastermind_mastermind@proton[.]me). - There is a
.onionURL in a Meet invite (https[:]//calendar.google[.]com/calendar/event?eid=NXQ5czNpajBtNmZsczgzcTBxM3JrZmwxcG4gbWFzdGVybWluZF9tYXN0ZXJtaW5kQHByb3Rvbi5tZQ&ctz=GMT+01:00):Hi everyone, our meeting in Switzerland is coming soon. I will give you the meeting place at the last minute, this will be safer.
Our agenda for this meeting :
- Give the package all details about the mission, and explain her what is at stake for our contact in Asia ;
- Define the route you will follow and where to drop the package, which will allow us to conclude the mission ;
I will await you. O. will be with me, that will allow us to talk about the http[:]//nvnomrsfvy3dcq25c5y2stgbptt4dcuiaidugy63zca2vc5vnhetaoad[.]onion/ site. @Associate, you will be able to tell her what you need on that website. I need you to confirm the appointment ASAP.
- The website can be visited using Tor. A flag is hidden is the page’s source.
Decentralized
- We search the following address
0x64D0D945AE5a384c18A3876064816b7E141980E7(found on the.onionwebsite) in ETH Explorer. - We find this transaction: https[:]//etherscan[.]io/tx/0x0f81151afd64b7b3fdda7dbd898d9f68840c5e58c3dc208b6504c798d6c9753a
- Displaying the input data in UTF-8 shows:
contact mail :
tsuyo63@proton.me
code name : Bruised Rogue - Let’s use Nexelat’s API again with this new code name: http[:]//217.182.69.14:8000/mm/bruised_rogue
{ "mission_name": "bruised_rogue", "description": "This mission has been triggered by <confidential> in 2022. The main goal is to make Lucilhe Dumarquais escape during her transfer to the court. <confidential> want to put her in a safe place and recruit her for her skills. We must drop her at <confidential> using a safe route. If we ever get caught during the mission, the order is to kill her, <confidential> identity is the main objective to be protected." }
Kanagawa
- Let’s dig deeper the address found earlier (
0x64D0D945AE5a384c18A3876064816b7E141980E7). - The logo found on the
.onionwebsite can be investigated too.
- https[:]//opensea[.]io/assets/ethereum/0x495f947276749ce646f68ac8c248420045cb7b5e/45600288605355569432684790323838389341572314161561028917962474406085593661441
Good time
- Examinate further the Google Calendar event that contained the
.onionURL. - The organizer is:
mastermind_mastermind@proton.me(L.N. -> Lian Nussbaumer) - Invitation was sent to:
mincah_mm@proton.mevok_0lski@proton.me
- Meeting will take place on:
Friday, December 16th 2022 11:00 – 13:00 UTC - We can suppose Olga Volkoska will attend the meeting (Lian Nussbaumer writes that “O. will be with him”) and that the Associate is mincah_mm.
- Let’s run
WhatsMyNameon every found pseudonym: mastermind_mastermind, vok_0lski and mincah_mm. - A TripAdvisor profile matched mincah_mm: https[:]//www.tripadvisor[.]com/Profile/mincah_mm
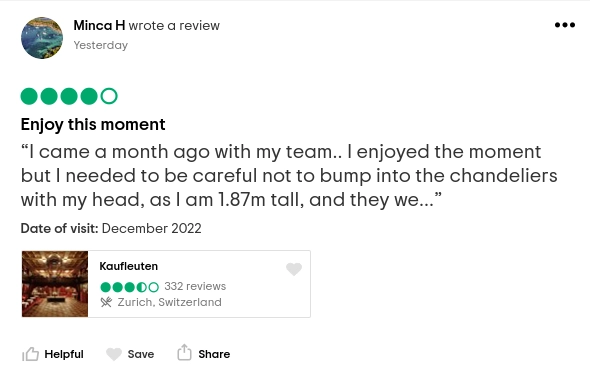
- Interesting information to keep in mind: Minca H. is 1.87m tall.
2. The Developer
Programming
- https[:]//web.archive[.]org/web/20230105145658/nelexat.ch/
- In the website’s footer:
made by Olga Vokolska - Let’s search GitHub with potential usernames.
ovokolskafound! - Interesting information to keep in mind: the GitHub biography shows another username: littleSparr0w
Listen to your heart
- Olga Volkoska starred a Mastodon client repository: https[:]//github[.]com/OVokolska?tab=stars
- We can search for Olga’s Mastodon profile using her usernames. littleSparr0w matched! https[:]//cyberplace[.]social/@littlesparr0w
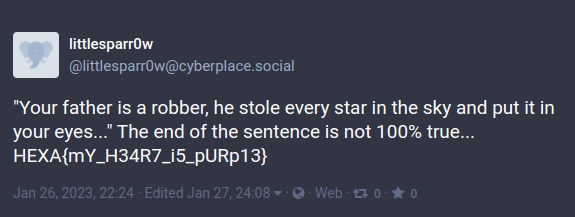
- Interesting information to keep in mind: she is 19 and her father is a robber.
3. Action Man
Hijacking
- A simple Google Lens search solved the challenge.
Fast and furious

Fly me to the moon
- Search for
FSF145Pwritten of the paper: https[:]//flightaware[.]com/live/flight/FSF145P
Chocolate
- Swiss + tram + Dolmetsch -> Zurich
- https[:]//www.google[.]com/maps/@47.3757964,8.5433349,2a,55.6y,91.91h,68.78t/data=!3m6!1e1!3m4!1shFGVEbph1u4LwMPFVd-xxQ!2e0!7i13312!8i6656
Bonbon
- The challenge’s attachment contains EXIF data:
GPS Latitude : 35 deg 31' 1.82" N GPS Longitude : 24 deg 1' 3.11" E GPS Position : 35 deg 31' 1.82" N, 24 deg 1' 3.11" E - Ag. Markou 8, Chania 731 32, Greece
- But pay attention to:
Still 142km to go until the airport near the fortress
- Heraklion International Airport “Nikos Kazantzakis” is 142 km from the location and is situated next to the Heraklion fortress.
Sovereign City
We will land at way 646940106, then we plan to hide near node 1803847939. Before we leave the city, we will change our car near way 22762642. After that, relation 8810294 will allow us to leave the city by staying on the left lane.
- “Node”? “Way”? “Relation”? This can only mean one thing: OpenStreetMap.
- Land: https[:]//www.openstreetmap[.]org/node/646940106 (Bretagne)
- Hide near node: https[:]//www.openstreetmap[.]org/node/1803847939 (Hougang, Singapour)
- Way: https[:]//www.openstreetmap[.]org/way/22762642 (Singapour)
- Relation: https[:]//www.openstreetmap[.]org/relation/8810294
- They travel to Johor Bahru in Malaysia.
Original
For this challenge, we have to find which file among 12 reports was written by a human.
Report 8 contains mistakes (“this crimes”), non-Latin characters (“Złodziej cieni”), and a lower level of English compared to the others.
Final countdown
- Malaysia, building in zone 4 with a religious site nearby + more than 3 km from the sea + a football field within a 5-minute walk from the building.
- Check zone 4 from the
Zones.kmlfile found on the.onion-> around Marang (useful tool: https://www.gpsvisualizer.com/map?output_home). - We will use Overpass Turbo to query the OpenStreetMap API: https://overpass-turbo.eu/
- The only matching node: https://www.openstreetmap.org/node/3975813161
Node: Masjid Abdul Rahman Limbong (3975813161) Location: 5.2221805, 103.0290490
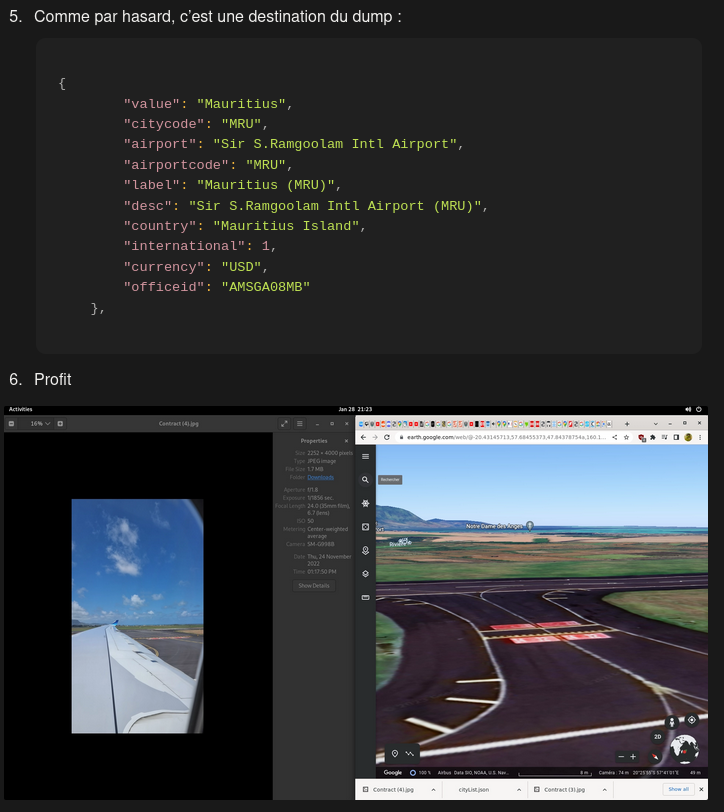
4. The Associate
The contract
- Garuda Airlines can be determined by the plane’s wing design.
- We try to retrieve the list of destinations served by the airline from the official website: https[:]//www.garuda-indonesia[.]com/other-countries/en/index. The list is hardcoded as a JavaScript object in the page source. We retrieve it as a JSON to use it later.
- On the airport runway, the markings “14 32” are painted in red. This means there is a runway oriented 14/32 (large white numbers) and another one or an access path marked with red numbers. Next, we use Google (especially Google Maps/Earth). After checking all international airports, we find Mauritius.
- It’s a destination listed in the JSON dump:
{ "value": "Mauritius", "citycode": "MRU", "airport": "Sir S.Ramgoolam Intl Airport", "airportcode": "MRU", "label": "Mauritius (MRU)", "desc": "Sir S.Ramgoolam Intl Airport (MRU)", "country": "Mauritius Island", "international": 1, "currency": "USD", "officeid": "AMSGA08MB" }
Wonderful excerpt from the original write-up which still make me laugh:
Impersonator
The only notes I have, sorry:

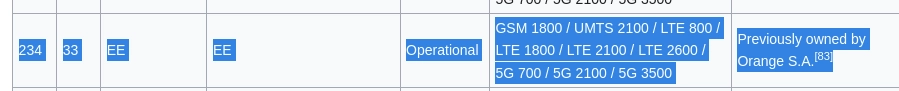
- https[:]//opencellid[.]org/#zoom=18&lat=51.487479&lon=-0.169462
Setup
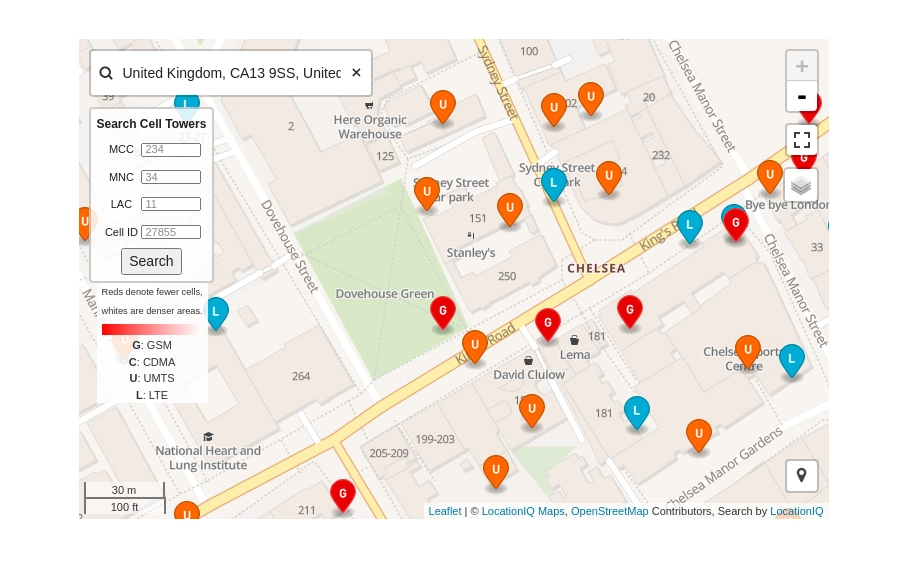
Current missions:
- Bruised Rogue (ordered by Tsuzune Y.) → package to be delivered soon
- Northern Silver (ordered by Basile M.) → waiting mission description
Services being claimed:- Due strike (ordered by Senator O.) → Law under examination at congress
- Aeric fusion (ordered by MastermindAlly3743) → Contract signed - stock market going to drop soon
- We tried “Northern Silver” in the FastAPI but it gave nothing.
- We searched the watch with Google (query: “festina timeless chronograph bleu bracelet cuir”): https[:]//www.notonlywatches[.]it/fr/montre-festina-timeless-chronograph-homme-bleu-cuir-dore-f20286-3-1427.html
5. The Intruder
The Intruder
He could be among you […] has a youtube channel
- First idea was to search in the Discord members or the CTFd players. And it worked!
- One CTFd account whose username was Pinkerton (https[:]//hexactf.ctfd[.]io/users/109) linked their YouTube channel: https[:]//www.youtube[.]com/@Pinkerton91/featured
Infiltration
- There are shorts on Pinkerton’s YouTube channel. We can suppose they have a TikTok account.
- Yes, they have! https[:]//www.tiktok[.]com/@user545947198194
- And it leads to a Discord server: discord[.]gg/unsb62pMc7
- The flag is in the bot’s welcoming message.
Sneak beak
Once in Pinkerton’s Discord, a series of challenges must be solved to get more flags.
-
We start easy. During my investigations I was able to find a recording. Can you tell me what is the title of what the protagonist sings? It will certainly help me to direct me on his nationality. (format: !c1-track_artist)
Song identified using the sound search feature in the Google Android app.
Flag!c1-LEMONADE_bonobosCongratulations ! You found the right answer - the first part for the command to get the hulotte role is : !yxmdvbn5j
Concatenate this part with the other one to create the command to execute and get the role
-
I want to be sure you are qualified to help me. Tell me how much someone risk in France if they make an identity theft by giving me the penal code article identifier. (format: !c2-123-1-1)
Flag!c2-226-4-1Congratulations ! You found the right answer - the second part of the command to get the hulotte role is : vwnnjy3htfe Concatenate this part with the other one to create the command to execute and get the role
Grow owlder
-
A friend of mine have clients in Europe. One of his clients asked to delete every pieces of information my friend has collected about him/her. My friend didn’t took care of that request but received a big fine several weeks after that. Could you help me find the law and article that can explain this fine? (format : !c3-RULE-1111)
Flag!c3-GDPR-17Congratulations ! You found the right answer - the first part of the command to get the effraie role is : !z7i2vj2 Concatenate this part with the other ones to create the command to execute and get the role
-
I heard from an US federal agency that there is a lot of inflation on food price in US last year, could you find the exact percent change for Month-to-month October 2022 to November 2022 on eggs? (format : !c4-1111 - percentage with no separator - example : answer is 5,3, just send !c4-53)
Flag!c4-23Congratulations ! You found the right answer - the second part of the command to get the effraie role is : ger6vf Concatenate this part with the other ones to create the command to execute and get the role
-
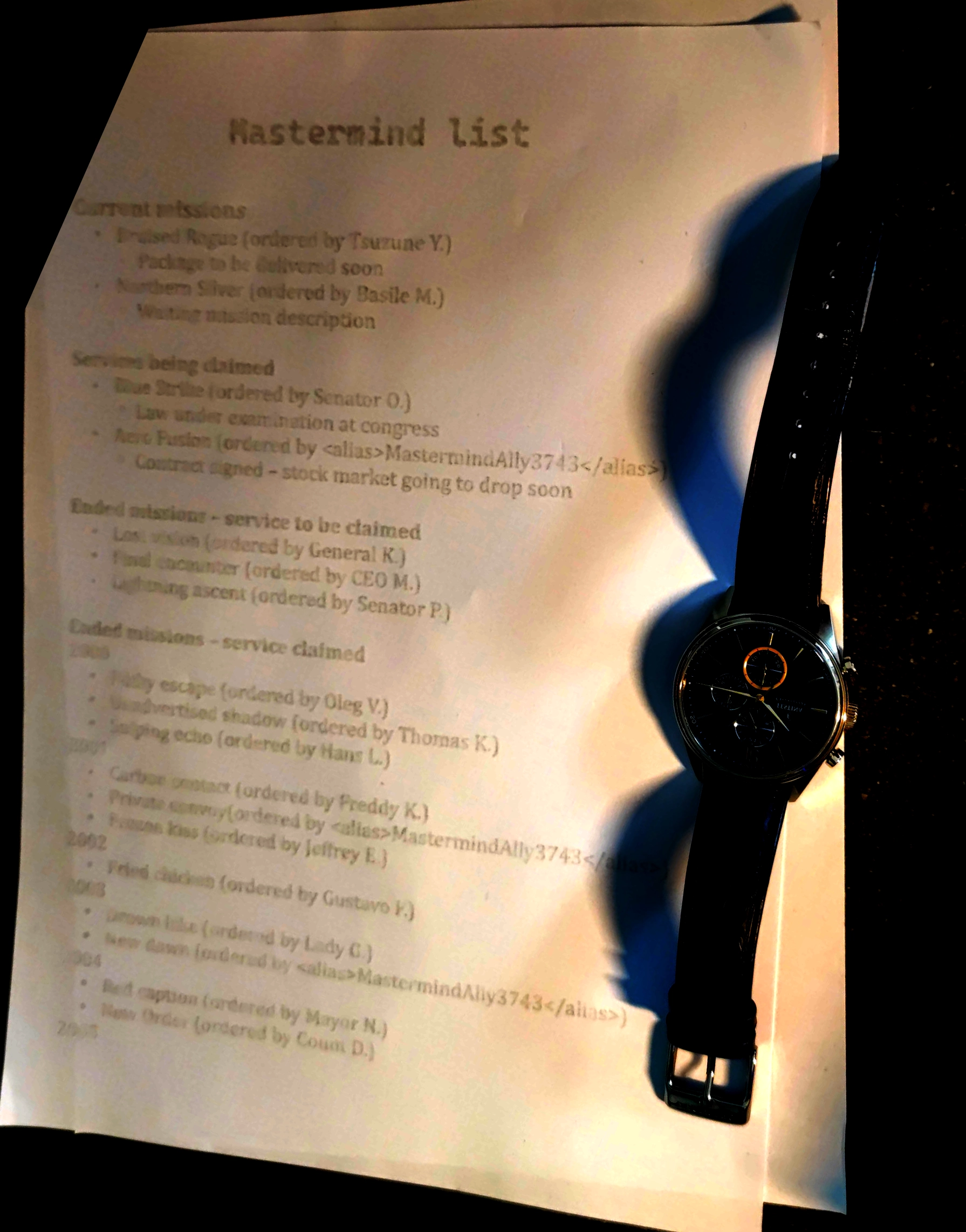
I am working on a very important OSINT case. A contact sent me an image from a camera filming adriatic sea, but couldn’t give me the source… My contact just told me that the camera is set on an hotel in Veneto, maybe that will help you to find this camera. One more thing… From this camera, we can see a panel where “Fantasy” is written. If you can find this camera, give me the phone number of the hotel (format: !c5-39XXXXXXXXXX)
Flag!c5-390415540660- Search for “fantasy” in the Veneto region in Italy. There is a “Pizzeria Fantasy” with a nearby webcam. Looking closely at the image, a “Fantasy” sign can be spotted in the bottom right.
- Hotel Ambasciatori: https[:]//www.sottomarina[.]net/webcam_sottomarina_chioggia.htm
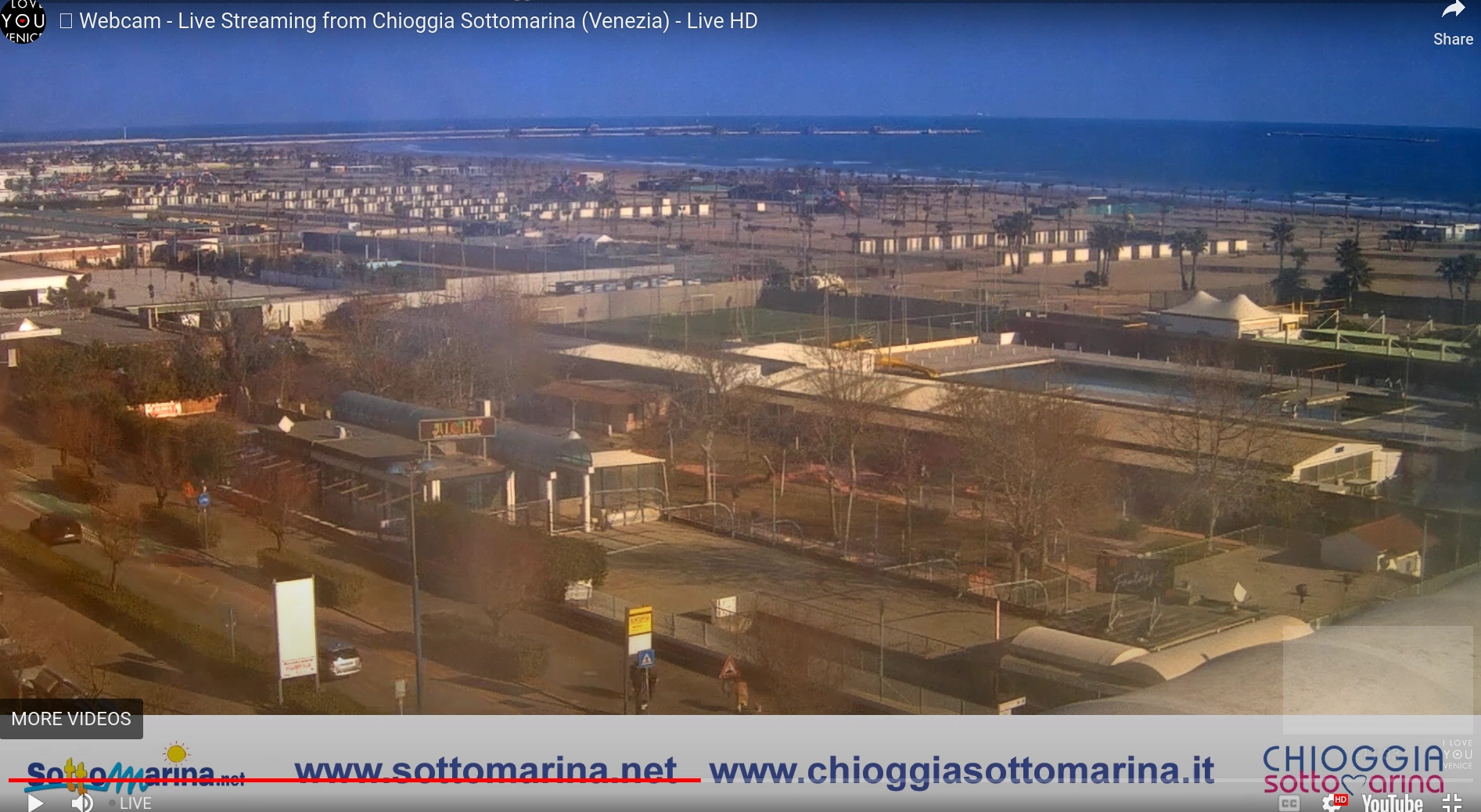
 OuchReading this in 2026, I still remember this challenge and solving it very early in the morning after hours of despair.
OuchReading this in 2026, I still remember this challenge and solving it very early in the morning after hours of despair.
Congratulations ! You found the right answer - the third part of the command to get the effraie role is : pjje2dd Concatenate this part with the other ones to create the command to execute and get the role
Tell me owl your secrets (not solved)
-
You helped me find where the guy singing in challenge 1 is coming from… This guy is Japanese and I managed to find his name : Tsuzune Yokoyama. Could you help me find a social network page where we can get more information about him, like his birthdate? (format : !c6-DDMMYYYY)
- His email from previous challenge:
tsuyo63@proton.me
- His email from previous challenge:
-
We have been working together for quite a moment now, you want to know me better? I will tell you more if you can find my Discord unique identifier (Discord ID) (format: !c7-11111)
Flag!c7-1055577878022070302Congratulations ! You found the right answer - the second part of the command to get the tengmalm role is : 63wv5fscmt Concatenate this part with the other one to create the command to execute and get the role
-
I had a video call with a contact who was supposed to give me information about a company doing business with someone related to my investigation. Sadly the call ended abruptly and I am not able to reach him at the moment. The good news is I have recorded the beginning of the call. The only things I know are that the company is probably part of the medical industry, and my contact found an SSID related to that company.
Can you find the name of the SSID I’m looking for ? (format: !c8-SSID without spaces)
- We found a database containing SSID and DrayTrek OUI but lacked time to solve the challenge.
6. Sidequest
He is back
- Google searches: “Kermit the third”, “Kermit III”. -> We get “Kermit Roosevelt III”.
- The genealogy can be found here: https://en.wikipedia.org/wiki/Roosevelt_family
- Kermit’s grandfather published a boot in 1919 (https[:]//annas-archive[.]org/md5/ff09af9d5886807ab0c130384f3810af)
- We retrieve the list of his books from his official website:
- https[:]//kermitroosevelt[.]net/books-2/
- First novel: In the Shadow of the Law: A Novel (2005)
- Second novel: Allegiance: A Novel (2015)
- The main character is Caswell “Cash” Harrison
- There is no movie or film project based on this book, so we can assume the author might have mentioned which actor could fit his character in an obscure interview.
- We listen to and read numerous interviews of the author about his book.
- After hours of interviews, we luckily come across one on the Harvardwood website:
“Cash Harrison is truly my bigger and more violent alter ego,” larks Roosevelt, “although I can see him being played on the big screen by someone quietly charismatic like Joseph Gordon-Levitt.”
He is back 2
- Google it. Find “sterane” scientific name.
6. Conclusion
Our team Holy fun king bingle :3 placed 14th out of 117 teams.
I have fond memories of this CTF, which really stood out, especially towards the end, as it required genuinely profiling the protagonists and understanding the storyline.
❤️ Thanks to my friends and team mates: nol, Schmingus and wil.