HeroCTF v7
1. Summary
| Event | HeroCTF v7 |
| Organizer | HeroCTF |
| Dates | From 28/11/2025 to 30/11/2025 |
| Type and Format | Jeopardy, remote |
| Team name | RisingStars |
| Rank | 91/1052 |
2. CTF and Organizer
HeroCTF is an annual cybersecurity online competition featuring a wide variety of challenges. Top teams are awarded prizes.

3. Challenges
Android
This was the first time I tried mobile challenges! The setup (downloading and installing Android Studio, JADX and Frida) took some time. Maybe even more than solving. 😅
1. Freeda Simple Hook
Try to find the password to open this vault!
Don’t waste too much time statically analyzing the application; there are much faster ways.
- The challenge title is explicit: use Frida. First, we open the attached APK in JADX to look for a function to hook.
get_flag()looks like a good choice.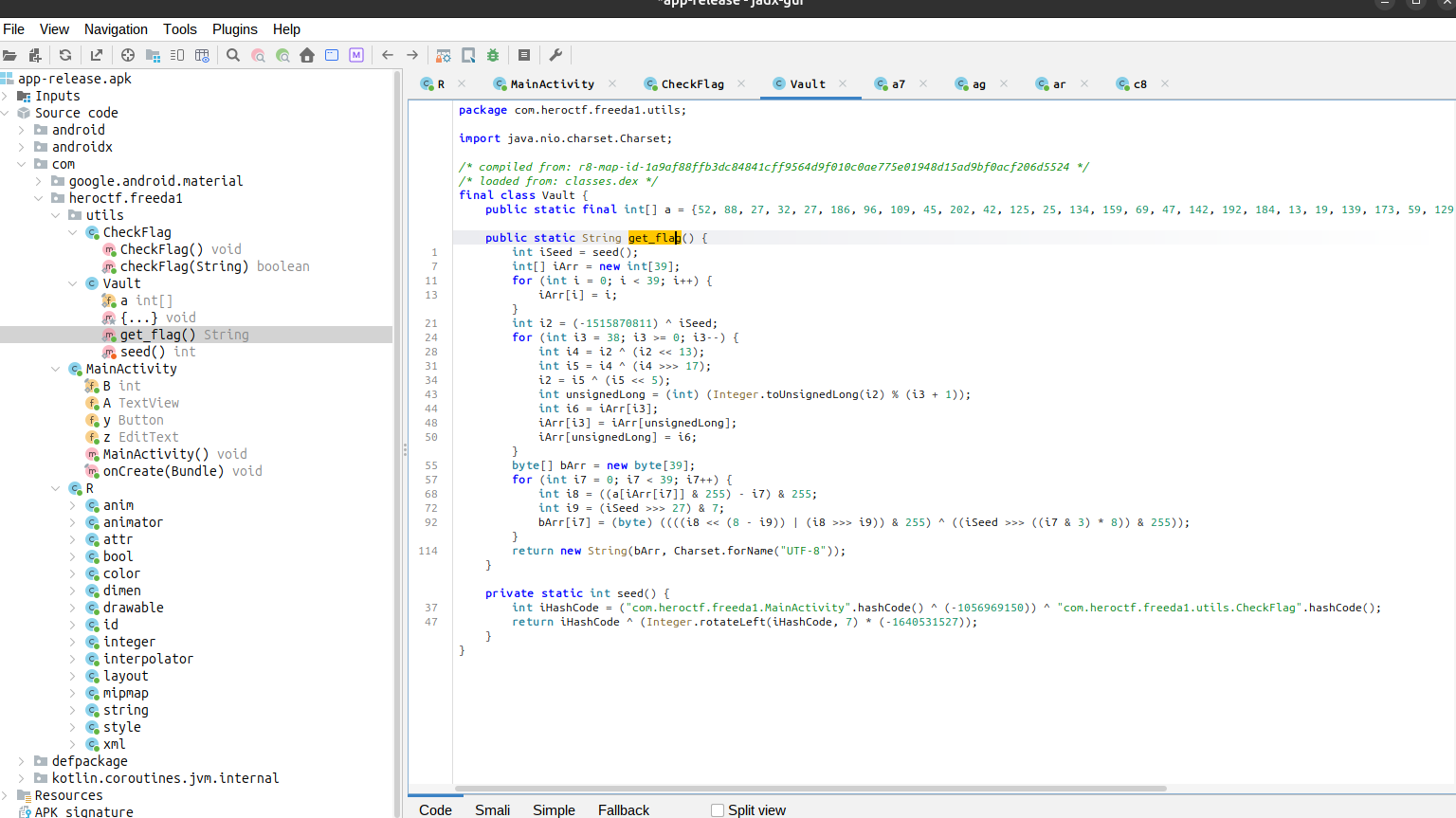
- The script that will run everytime
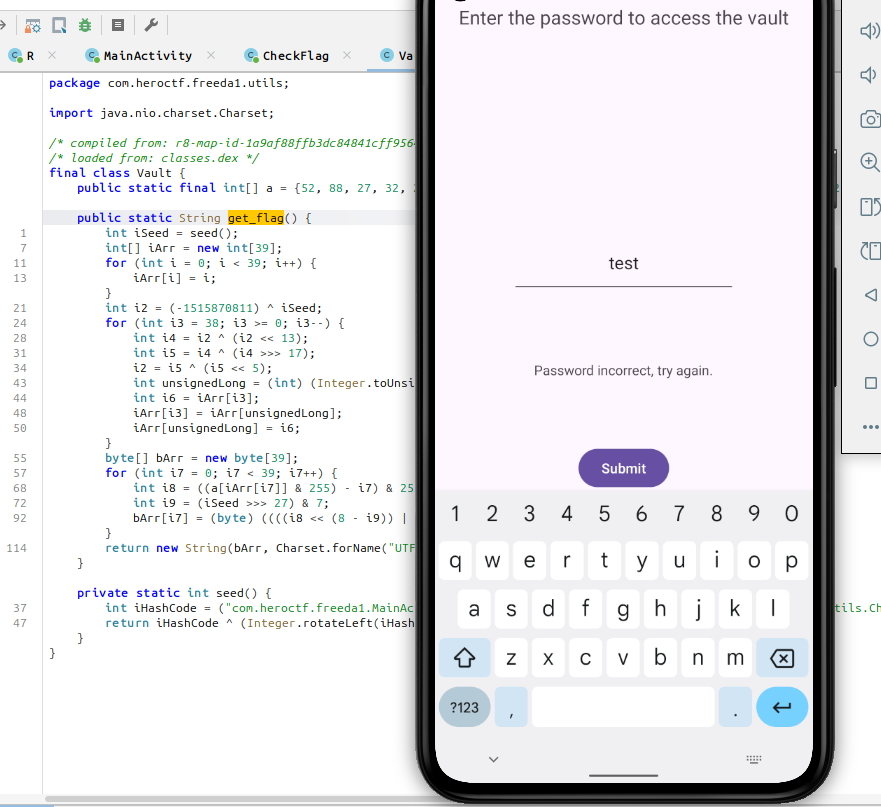
get_flag()is called:Java.perform(function () { var Vault = Java.use("com.heroctf.freeda1.utils.Vault"); Vault["get_flag"].implementation = function () { console.log(`Vault.get_flag is called`); let result = this["get_flag"](); console.log(`Vault.get_flag result=${result}`); return result; }; }); - We can emulate a smartphone with Android Studio to install the APK.
$ adb install <app>.apk - We run Frida server and check the application name:
$ frida-ps -Uai PID Name Identifier ---- ------------------ --------------------------------------- 5291 Freeda1 com.heroctf.freeda1 - On our host, we run Frida client with the script created earlier:
$ frida -U -l <script>.js -f com.heroctf.freeda1 - We can type any password to trigger the hooked function and get the flag:
2. Freeda Not Root
Try to find the password to open this vault!
I was told that it was dangerous to let my application install on a rooted machine. I fixed the problem!
Don’t waste too much time statically analyzing the application; there are much faster ways.
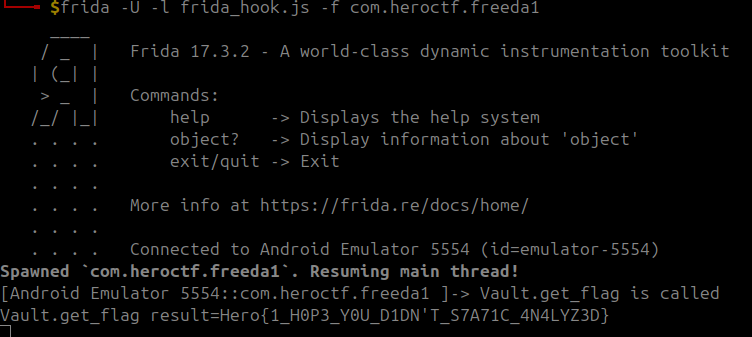
This challenge was not so different from the previous one.
- This time, we also have to hook
detectRoot(). - The JavaScript script to hook the function:
Java.perform(function () { var Security = Java.use("com.heroctf.freeda2.utils.Security"); Security["detectRoot"].implementation = function (context) { console.log(`Security.detectRoot is called: context=${context}`); let result = this["detectRoot"](context); console.log(`Security.detectRoot result=${result}`); return !result; }; var Vault = Java.use("com.heroctf.freeda2.utils.Vault"); Vault["get_flag"].implementation = function () { console.log(`Vault.get_flag is called`); let result = this["get_flag"](); console.log(`Vault.get_flag result=${result}`); return result; }; });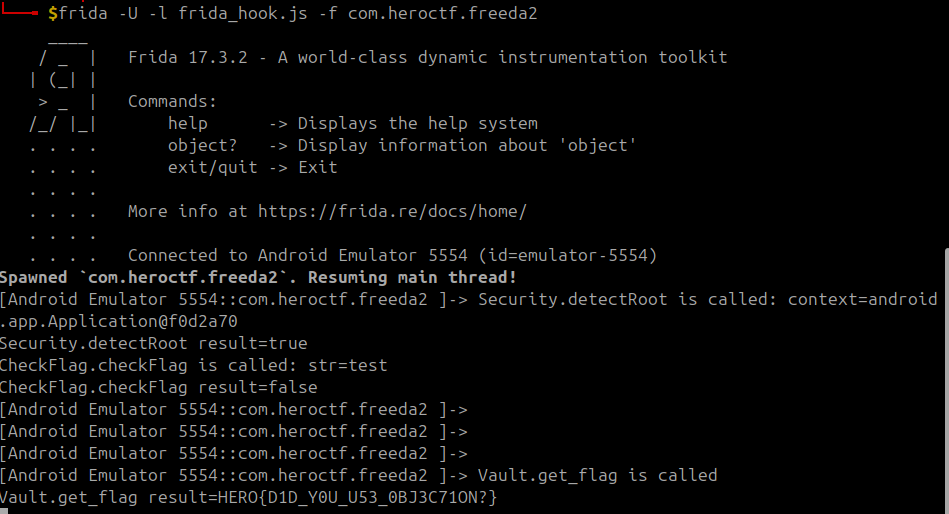
Forensics
1. Operation Pensieve Breach 1
The SOC of the Ministry of Magic received multiple critical alerts from the Domain Controller.
Everything seems to be out of control.
It seems that a critical user has been compromised and is performing nasty magic using the DCsync spell.
You’re mandated to investigate the Principal Domain Controller event logs to find:
- sAMAccountName (lowercase) of the compromised account performing bad stuff.
- Timestamp of the beginning of the attack, format: DD/MM/YYYY-11:22:33 SystemTime.
- Source IP address used for this attack.
- The last legitimate IP used to login before the attack.
The findings have to be separated by a “;”.
ministry_winevt.7z
Here is an example flag format:
Hero{john.stark;DD/MM/YYYY-11:22:33;127.0.0.1;127.0.0.1}
I remember enjoying this challenge because I didn’t know anything about Windows logs and took time reading documentation to solve the challenge.
- Requirements:
sudo apt-get install libevtx-utils evtxexport -f xml Security.evtx > Security.xml - The account performing the DCSync attack is albus.dumbledore, as identified by Event ID 4662.
- From the logs, we can clearly see that this account grants itself privileges right after an anonymous login from the IP address:
192.168.56.200. - Then, someone logs into the albus.dumbledore account and begins the attack from
192.168.56.200at23/11/2025-00:13:41. - The only other IP address from which albus.dumbledore has logged in is
192.168.56.1.
Resources:
- https://omerbenamram.github.io/evtx/
- https://www.ultimatewindowssecurity.com/securitylog/encyclopedia/default.aspx
- https://wiki.sans.blue/#!Tools/WindowsEventLogsTable.md
Reverse
1. The Chef’s Secret Recipe
Open the file in a decompiler such as Ghidra. The program expects a list of ingredients. Each ingredient is actually the name of a function called at that point. We can clearly see the code type, which is a function pointer on ARM. Each function returns a number. These are ASCII codes which, once converted, directly reveal the flag.
4. Conclusion
Still one of the most fun CTF event! Sadly, I couldn’t attend the whole event (having a life, you know).
❤️ Huge thanks to my team mates: Duma999, Pioupia (and the others who preferred to remain anon).